The Shadow Explorer of Z-VSScopy can open and search unmountable shadow copies and system restore points.
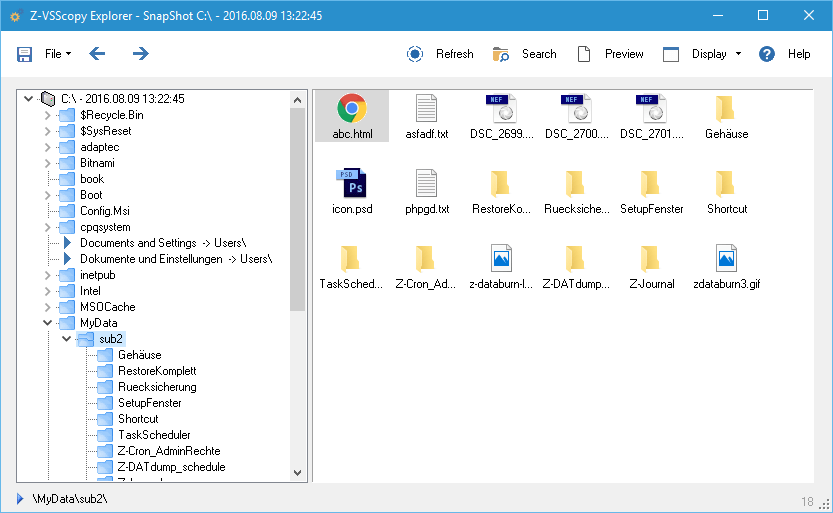
Features of the Shadow Explorers
With the Shadow Explorer you can search fo files using wildcards to easily find the files you are looking for.
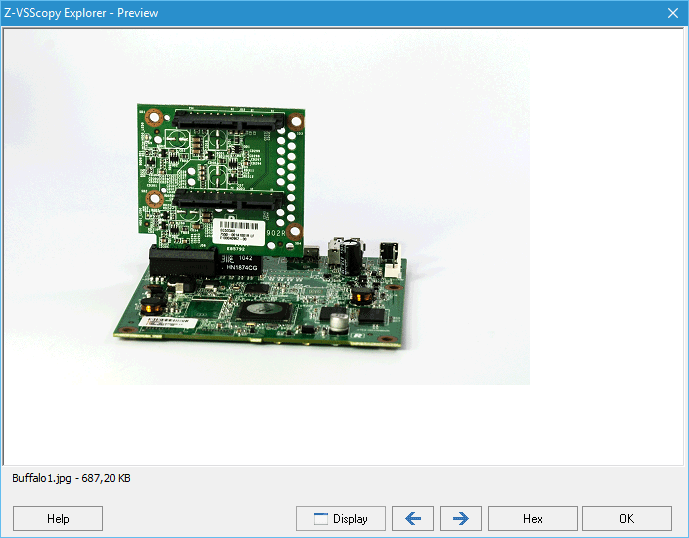
A preview window can be opened for every file, displaying a preview image with the option to display the files bytes in hexadecimal numbers. e.g. to check if all bytes in a file are ‘null’.
Files and Directories can be exported from a snapshot (a shadow copy or system restore point). This allows you to restore an older version of a file that has been saved in a snapshot.
Mit dem Laden des Videos akzeptieren Sie die Datenschutzerklärung von YouTube.
Mehr erfahren
VSSadmin Protect
Crypto viruses often start attacking a system by deleting all shadow copies and system restore points to hinder anyone from restoring encrypted files using the automatically created snapshots. To appear harmless to malware detectors they often use the Windows command line tools vssadmin.exe and wmic.exe to do so.
Z-VSScopy can prevent other programs from using those two commands without resticting general system functionality. To do so, the program has to make certain alterations to the operating system. After that all access calls to vssadmin.exe and wmic.exe will be logged in a special monitoring log file. This way you can check what programs are trying to access these commands.